Introduction
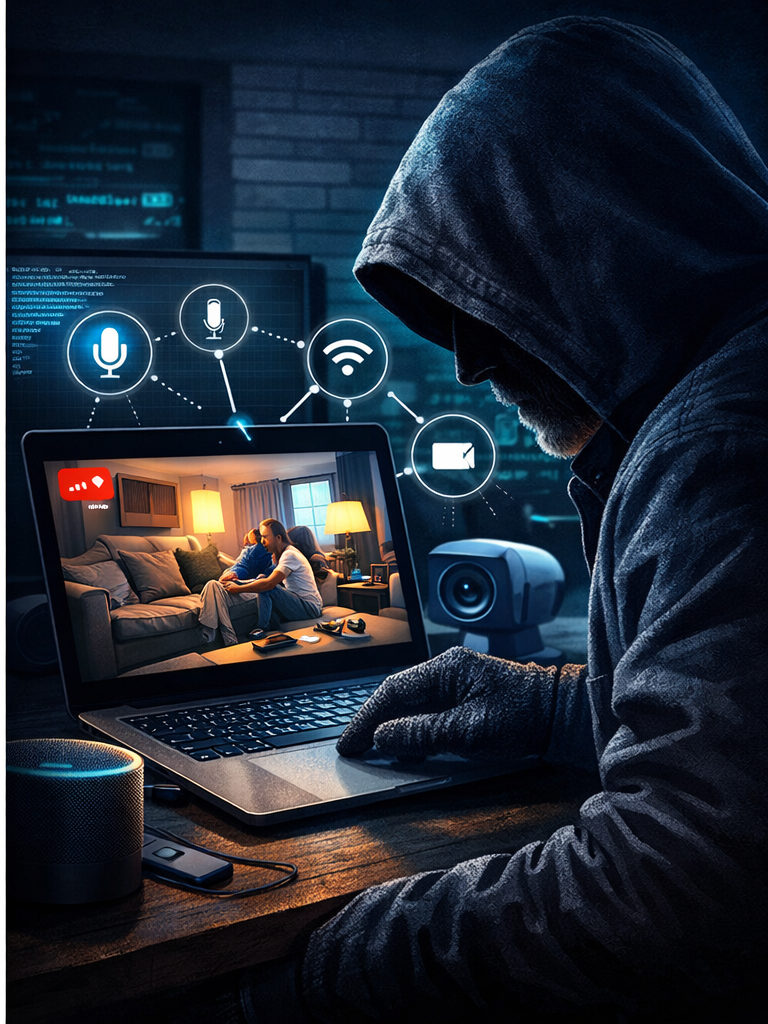
The rapid adoption of smart home technologies across Australia has transformed everyday living. Devices such as smart TVs, streaming boxes, and connected IoT systems offer convenience and seamless connectivity. However, these same technologies are increasingly being exploited by cybercriminals.
A recent large-scale cyber incident, known as KimWolf, demonstrates how millions of household devices can be silently compromised and used as part of a global cybercrime infrastructure. This case highlights the urgent need for cybersecurity awareness and education, particularly as the number of connected devices continues to grow.
What Is the KimWolf Botnet?
The KimWolf operation exposed a sophisticated botnet that infected more than two million Android-based devices worldwide. These included commonly used household technologies such as smart televisions and streaming devices.
Attackers exploited software vulnerabilities to gain unauthorised access and convert these devices into proxy servers. This allowed them to route malicious internet traffic through residential IP addresses, making cyberattacks appear legitimate and significantly harder to detect.
The increasing integration of IoT systems has expanded the global attack surface, making both individuals and organisations more vulnerable to cyber threats.
How Cybercriminals Exploit Smart Devices
Once compromised, devices can be used for a range of malicious activities:
- Distributed Denial-of-Service (DDoS) Attacks
Botnets can overwhelm systems by sending massive volumes of traffic, disrupting websites and online services.
- Credential Stuffing
Attackers use stolen login credentials to gain unauthorised access to accounts across multiple platforms.
- Residential Proxy Abuse
By using legitimate home IP addresses, attackers can bypass traditional cybersecurity filters and mask their identity.
This reflects a broader shift in cybercrime tactics, where attackers increasingly exploit trusted environments rather than external systems.
The Business Model Behind Modern Botnets
One of the most concerning aspects of botnet operations is their monetisation strategy. Cybercriminals are no longer just disrupting systems; they are building scalable, profit-driven infrastructures.
In the KimWolf case, compromised devices were used to sell internet bandwidth via proxy services. This effectively turned unsuspecting users into unwitting participants in cybercrime networks.
This trend aligns with research showing that cybersecurity risks are increasing alongside digital transformation and connected technologies.
Why This Matters for Australian Households and Businesses
For Individuals
- Slower internet performance
- Privacy breaches
- Potential legal implications from criminal activity linked to your IP address
For Organisations
- Increased attack surface from employee-owned devices
- Risk of network infiltration through unsecured IoT devices
- Difficulty detecting malicious traffic disguised as legitimate users
Cybersecurity is fundamentally about protecting the confidentiality, integrity, and availability of information, which are increasingly at risk in IoT environments.
How to Protect Your Devices and Network
For Individuals
- Purchase devices from reputable manufacturers
- Regularly update firmware and software
- Disable unnecessary remote access features
- Secure your home Wi-Fi network
For Organisations
- Implement network segmentation
- Apply zero-trust security principles
- Monitor network traffic continuously
- Educate staff on IoT-related risks
Cybersecurity awareness and education play a critical role in reducing vulnerabilities, particularly for individuals and small organisations with limited resources.
The Role of Cybersecurity Education
As cyber threats evolve, education becomes a key defence mechanism. Users must understand not only how attacks occur, but also how their own devices can be exploited.
For institutions like Academic Education, integrating real-world scenarios such as IoT botnets into curriculum design helps students develop practical cybersecurity awareness and skills.
Training and continuous learning are essential, as both technical vulnerabilities and human factors contribute to cyber risk exposure.
Conclusion
The KimWolf botnet serves as a clear example of how everyday technology can be weaponised at scale. As smart devices become more embedded in daily life, the boundary between convenience and vulnerability continues to blur.
Addressing this challenge requires a combination of user awareness, secure device management, and structured cybersecurity education. Without these measures, even the most ordinary household device can become part of a global cybercrime network.